2020 Is Not Over Yet, but We Already Know Your Favorite Passwords
Just like every past year, the info security community completed its end-of-year evaluation of password practices and user habits. Sadly, the overview for 2020 is not particularly encouraging.
There is a large amount of advice on the Internet concerning password security. Our own articles deal with the subject very often. However, it seems people are particularly stubborn when it comes to passwords and simply refuse to listen and learn.
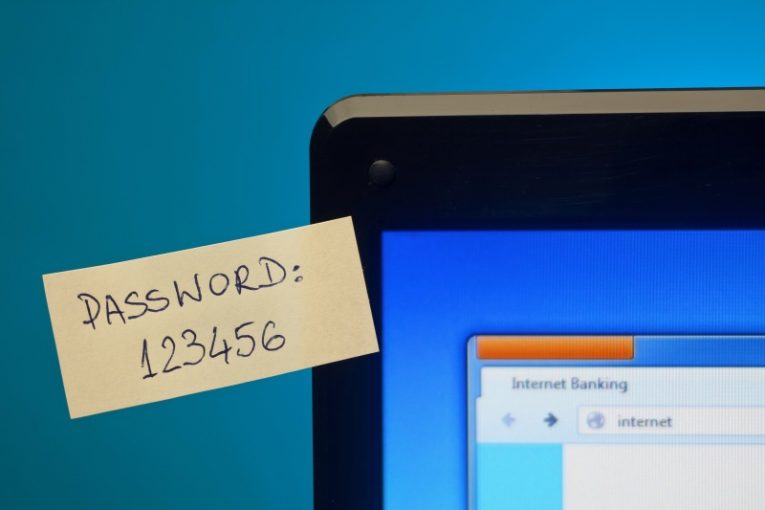
Believe it or not, "123456" is still the most common password among the people polled in the password security survey. Security researchers would usually publish a metric describing estimated password strength - "time to brute-force", which refers to how long a hacker or a body of bad actors would need to crack a particular password. That metric isn't even applicable when it comes to passwords such as "123456", as the password is that overused, easy to guess and obvious.
The second spot in the password hall of shame is reserved for "123456789". It seems people still somehow think that stringing more consecutive numbers one after the other makes their password more secure. This is simply not the case and has never been.
Other long-standing hall of shame classic password strings such as the word "password" still come up in the top 10 most commonly used passwords for the year 2020. The only password on the top 10 list that is not guessable by a brute-force script within a matter of seconds is "picture1". Sadly, the time it would take a regular home computer to brute-force a password like "picture1" is a couple of hours, which still means the password is far from secure.
It seems people almost grasp some of the principles of good passwords but never really implement them well, like the ham-fisted attempt to mix letters and numbers in the string.
What is the difference between a second and several centuries?
To give some sort of perspective on password strength, we came up with a test password that uses a mash-up of two unusual words, resulting in a string not found in a dictionary, with multiple symbols and numbers thrown in the mix, and ran the resulting 18-character string through a password strength checker. The outcome was that it would take an estimated hundreds and hundreds of years to brute-force this string, even when using a large compute network, making it effectively uncrackable.
It doesn't always take a 20-symbol string to have a safe password, it just takes mixing letters, symbols and numbers in good measure and never using simple words that you can find in the dictionary, as most brute-force scripts rely on massive dictionary databases to crack passwords.